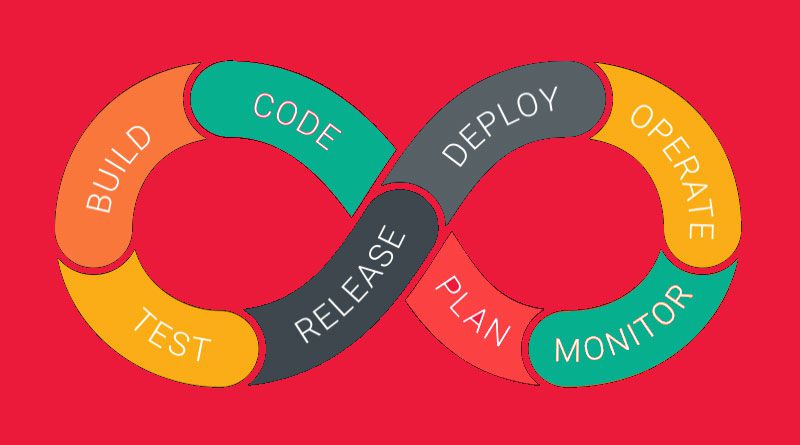
Many teams tasked with software projects are taking steps to move towards the DevOps model because of the inherent advantages that come with it. In the DevOps model, the Dev and Ops teams work in close collaboration. The IT industry is recognizing that cybersecurity threats are alarming, and it is time to take action. With this, the DevSecOps model is coming to the rescue.
In the DevSecOps, there is an amalgamation of the Developers, Operations, and Security. Eventually, with such an approach, IT Security is seamlessly integrated into the whole life cycle of the DevOps model. Moreover, the team becomes more consciously aware of security integration from start to end.
The team dynamics – everyone participates in the process of Security integration.
As the team integrates IT Security into the entire life cycle in the DevSecOps method, the whole team gets involved. The team, including software developers, QA testers, QA automation engineers, the Ops team, etc., share responsibility. Everyone will be held responsible and accountable.
There are cultural changes that come into the picture, and the team must be trained and guided to fully understand why this move is essential, as well as in the tools and techniques that can help. There will be additional tools embedded in the life cycle for built-in security.
Ideally, once the whole team is trained in security awareness, the team will start strategizing for the building of robust security controls. They executed their project-related tasks by taking into account risk tolerance, performing risk-benefit analysis, etc.
What will the integration of built-in security look like? The role of automation
In this case, there will be conscious planning of security integration involving the whole team. We know that no DevOps model is successful without automation. Hence, even in the case of the DevSecOps model, the team builds a plan around security-related automation. In the whole process, the security experts will be in charge of monitoring the security-related aspects, and at the same time continuously tracking the new data for security threats. There is a continuous feedback cycle that runs as well through the Developers, Operations, and the Security experts. Everyone is accountable for the success of DevSecOps deployment.
The team needs to find DevSecops tools that can be integrated into the pipeline such as Continuum Security, ThreatModeler, GitLab, etc. For instance, with the help of tools like GitLab, every code that is committed is scanned automatically for security vulnerabilities, including its dependencies. Additionally, results are presented to the developer for their quick action.
Also, the QA engineers and the developers need to use Development/Test automation tools that easily integrate with the 3rd party DevSecOps software. For instance, TestProject, Microfocus UFT, IBM RFT, etc., makes this possible. As a result, using a test automation platform that seamlessly blends in with the methodology of DevSecOps, makes the job of the team much easier. After all, automating the testing process is an essential DevSecOps practice.
Shifting Security Left – Integrate security early
DevSecOps encourages Shifting Security left – the actions taken with regards to developing security standards, techniques, etc., and even testing the security controls, happens early in the cycle. As a developer, it would be good to perform code analysis in the smallest chunks. The team needs to build the mindset of automating early and often. We need to keep in mind the importance of the DevSecOps practice which encourages consistent analysis of code.
Security scans always need to be conducted from the early part of the cycle, and continuously. The scans will expose any security flaws, if present so that they can be fixed as early as possible. Including automated penetration testing, configurations that are risky need to be identified and fixed early. Early testing results in early detection of vulnerabilities in the code.
Why and How do we make this move?
Considering the many security threats that are faced by software projects these days, DevSecOps is becoming more important to adapt to. The move is required to help secure several levels of the project. In each of the levels, privileges and controls are set up to prevent unauthorized access to situations such as the following.
Apart from preventing security breaches from happening, it is vital to train employees of any company on how they need to respond when or if a security breach occurs. Training and certifying the employees in your company in the area of security is vital for the business in the long run.
Data and database security and environment security
Even a wrongly configured database control can expose your company’s data to a cybersecurity attack. Any breach of security can expose important private data of users. Therefore, the system must be designed in such a way that such occurrences do not happen as ultimately the integrity of the business will be at risk. The company can include a strategy of network segmentation, and a well-thought architecture and internal infrastructure for security for optimal function.
CI/CD process security
The project would be required to move to automate the security-related scans and tests in the CI-CD process. The pipeline architecture should be well thought out as it will be a part of the high-level point of view in imparting security aspects into the whole system. A robust, secure deployment pipeline is of utmost priority. Security systems that deploy the code also ought to be ramped up along with ramping up the security of the code itself.
Access controls, and change control systems
Appropriate access controls ought to be set up, and any changes should be tracked automatically by the system. When there are changes that are submitted in the code, it is a good idea to increase the speed and efficiency of the method for how this change will be assessed to be good or bad. Practical and well-designed Change Management is an essential DevSecOps practice. Everyone should be made aware of any change that is made, and by whom it was made.
Cloud security
DevSecOps resolves many of the known challenges associated with cloud security. With regards to cloud security, the project needs to ensure that an assessment of the security features is performed in the cloud deployment levels. Accordingly, they would need to get encryption systems set-up, along with solving all the security concerns. Cloud penetration testing and security assessments are mandatory to strengthen cloud security.
Security reports and Monitoring
Reports need to be regularly and automatically scheduled using tools which display the risks in the system and fix them right away, as monitoring compliance to regulations is one of the vital aspects of DevSecOps practices. In the process of being ready for audits, and collecting associated compliance pieces of evidence in real-time whenever code is added or updated, it eventually enables the organization to be prepared for any security threat attacks. To implement continuous investigation of threats as the DevSecOps practice, the whole team will need to be trained to be knowledgeable of security scans, code reviews, penetration tests, etc.
Conclusion
The move to DevSecOps model is inherently a mindset change into integrating IT security into a project from start to end, as it becomes the foundation of the whole process. Eventually, the team ought to follow a 360-degree outlook in strengthening the security aspects of the DevOps environment to make it a successful implementation of the DevSecOps model. And most importantly, the security experts need to continuously be involved and mentor the Dev and Ops team while being responsible for designing and deploying a secure deployment pipeline to fit the best security standards.