They say “crime does not pay,” but for the cybercrime operators in this completely illegal industry run by malware developers, scammers, and cyber thieves, it looks like it does. For those that victimized through the years, especially those that have had insurmountable losses due to these cyberattacks, they paid too—and they paid a lot in ways more than money or data. Cybercrime is one of the digital world’s growing nightmares that have stuck and evolved together with the advent of its best accomplishments.
Real-world criminal activity is echoed digitally, as well. In both worlds, we find a plethora of scams hell-bent on stalking, stealing, extorting, and destroy. It should be condemned and all efforts exhausted both in real-time and real-life to combat this fully-operational, ever-expanding, billion-dollar criminal industry. In 2020, online fraud prevention investments will hit a 30% increase of $9.2 billion to combat cybercrime, which Juniper Research predicts will hit $25.6 billion in terms of online payment transaction fraud worldwide. That’s more than $16 million disparity between preventive efforts and the total amount that the cybercrime industry is expecting to get for this year alone. We see that cybercrime fighters need to rally their forces even more and level up in their efforts to protect the public against these threats.
Let’s look at theevolution of cybercrime through the years to get a better understanding of its destructive force:
Web of Cybercrime and its Key Players
First, let’s look at the players responsible for global losses amounting to hundreds of billions of dollars annually.
- Programmers: brains of the operations; develop exploits and malware, whether intentionally or not. Some programmers do not intend their products for cybercrime at all, while some developers certainly create programs for malicious purposes. Data stolen can come from various sources through phishing scams, email scams, data harvested from data breaches, even social media sites are used for fraudulent trading of bank details. Programmers can also buy these databases online in the dark web
- Distributors: responsible for buying and sellingstolen data
- Tech experts:in charge of IT infrastructure, servers, databases, and security for cybercriminals’ use
- Hackers: they are the cyber experts who look for vulnerabilities in systems, applications, and networks to exploit
- Fraudsters: are those that plot social engineering strategies for phishing scams
- Hosted systems providers: hosts illegal content servers and websites, whether knowingly or unknowingly
- Organization leaders: they are those that bring the whole operation together, like gathering the team and identifying vulnerabilities to attack and people to target
Cybercrime Operations: How Does it Work?
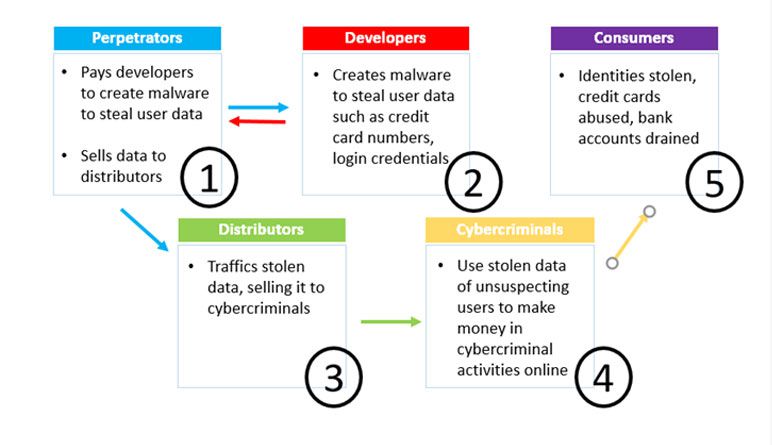
As seen in the illustration of this web of crime, Perpetrators steal information from users, hiring Developers to create malware online information theft. Perpetrators pass the data to Distributors, vouching for the credibility of cyberattack specialists in the field. They sell the stolen user information on the dark web to Cybercriminals who use it for fraudulent crimes such as credit card numbers, login credentials, and the like, to make money from victimized Customers.
The Evolution of Cybercrime in the Last Decade
Cybercrime evolved alongside eCommerce, as transactions are being done online more and more. Traditional criminals just saw another channel to exploit and modernized their operations into the digital marketplace as well. Here are some of the most severe threats the world has suffered in the last decade:
- The 1990s: “Nigerian Prince” and similar email scams
Cybercriminals continue to make money through email scams by ripping off unsuspecting, everyday people. The email can say a family member is in trouble or appeal to pity that someone from another location or the other side of the world is in need. Whatever the content of these emails, they are meant to trick people and conduct money heist.
- The 2000s: Money mule and eCommerce money-laundering schemes
Criminals “hired” unsuspecting people for what they thought were real jobs. Once hired, the criminals opened accounts in the “mules’” name, and had money transferred to these accounts. The mules were then instructed to withdraw the money and send it to another contact abroad via Western Union or MoneyGram. This money laundering activity proved effective as perpetrators were challenging to catch.
It evolved further into e-commerce scams where criminals buy stolen credit cards and credential login data harvested from data breaches for fraudulent transactions.
- The 2010s:Online poker and in-app video game cybercrimes
Online poker sites became a channel for laundering until the big FBI crackdown in 2011. Cybercriminals went after online poker players and their large bank accounts associated with their online gambling.
- The latest scams: Online free-to-play video games
Users are lured through free-to-play platformsthen offered in-game purchases once they’re addicted to the game. The in-game purchases give the players leverage like extra life, currency, and other added features and bonuses to strengthen the player’s character. It’s a billion-dollar industry and cybercriminals have used it to launder money, steal credit card data and retails them to the highest bidders on the dark web. Cybercriminals are also using cryptocurrencies to launder money and obscure their activities make all money movement untraceable. Once they have “cleaned” the funds, the criminals transfer the cryptocurrency into their bank accounts.
Online Fraud Predictions for 2020
- Deep fake technology used for identity fraud: Deep fake is a portmanteau of the words “deep learning” and “fake.” It is a branch of synthetic media that uses a machine learning technique called generative adversarial network or GAN. Invented by Ian Goodfellow in 2014, GAN can generate fake photos, audio, and video from existing data. It has gained global attention for its malicious uses like pornographic content, fake news, identity and financial fraud. Because it can spoof the human voice, it has been used to attack call centers or conduct email compromise scams. It is foreseen to defeat face recognition controls, including those using state of the art liveliness tests. Governments and industries need to develop silent, behind-the-scenes controls further to strengthen biometric authentication vulnerabilities.
- LiFi(Light Fidelity) networks targeted by hackers: LiFi is a wireless optical networking technology that uses light-emitting diodes (LEDs) for data transmission.It’s a high-speed Internet technology with higher speeds than Wi-Fi with 10,000 times the frequency spectrum of radio. LiFi is supposedly more secure because data cannot be intercepted without a direct line of sight. Commercial use is still underway for the LiFi, but just like any other network, it could be hackable as WiFi and can be prone to physical interferences that can be exploited by cyberattacks.
- Identity database attacks: IAM (Identity Access Management)provide each individual (e.g., employees and customers) their own unique digital identity. Access management uses identification, authentication, and authorization to establish, monitor, maintain and modifythe “access lifecycle” of each individual. This system makes it harder for cyber robbers to breach users’ data. Along with other efforts that banking systems are putting in place to protect their institutions and customers from both traditional fraud and cybertheft, like tighter controls over social engineering and use of PSD2, all make account takeover harder for cybercriminals. Hackers will focus their attention on identity databases, attempting to get multiple data points on each unsuspecting citizen.
- Identity Mules as accessories to cybercrimes: Identity mules are casual criminals “used by others to launder the proceeds of cybercrime by taking stolen money and goods and turning them into ‘clean’ funds. They do this via internet payments, money transfers, or online auctions.”Synthetic identity fraud is the fastest-growing financial cybercrime in the US, according to a Federal Reserve study, that shows it has an average charge-off balance per instance of $15,000.
- FinTech companies will be target by cyber thieves: The fintech sectorwill begin to see an increase in online fraud because they are less heavily regulated and are more agile to introduce new functionalities. However, the lack of proper defenses and access to the fraud consortium databases of the banking sector makes them all the more vulnerable.
- Chatbot and voice assistance payment fraud: Chatbots are conversational AI designed to simplify human interaction with computers so the latter can understand and respond to human input through voice or chat. Many financial institutions use such AI-based customer assistance tools, such as chatbots and voice-based interfaces, to prevent account takeover by cyber thieves. Chatbots turned fraudbots could pose threats such as spoofing/impersonating someone else, tampering of data, and data theft.
- Selfie biometric data theft and trade in the dark web: There’sa demand in the dark web for personalized biometric dataas more websites and applications are turning to selfie-based verification and modernising most of their operations and customer activities. This automation that supposedly should protect consumers’ data is also vulnerable to data breach and theft through phishing campaigns, ransomware and other cyberattacks meant to break into mobile device authentication.
Cybercrime Prevention is Better than Mitigation Cyberdefense systems are intensifying because cyberattacks are increasing. But cyberattacks are also intensifying in response to stricter, more rigid and comprehensive cyberdefense systems implemented nowadays. To catch a thief in the digital world is difficult, but not impossible. There is always a solution to solve threats and defeat cyberattackers, no matter how severe their fraudulent activities get. For instance, the banking industry is undergoing digital transformation to heighten its defense, even offense security systems. Vigilance is key, so cybersecurity tech needs to crank up all the security measures at its disposal continuously. For private individuals, arm yourselves with awareness and much-needed security know-how to keep your computer and online credentials safe and secure, like changing passwords, making them complicated, using password managers, multi-factor authentication, using VPN, and the best antivirus and security software for all owned devices. We owe it to ourselves to stay informed and protected.

